Online Higher Education Cybersecurity Conference
Cybersecurity For Higher Education
- Cybersecurity experts and speakers
- Higher Education institution attendees and presenters
- Knowledge sharing and affordable solutions
- Cybersecurity vendor expo meet and greet
- Higher Education Case Studies and Best Practices
Welcome to the Annual Cybersecurity Conference for Higher Educational Institutions! This event is designed to meet the unique cybersecurity needs of academic institutions.
Our conference brings together industry experts, leading academics, and cybersecurity professionals to foster collaboration, knowledge sharing, and preparedness in the face of evolving cyber threats.
With a focus on higher education, our conference aims to enhance cybersecurity awareness, knowledge, and practices among attendees. Through interactive sessions, expert presentations, and hands-on workshops, we provide valuable insight, practical strategies, and best practices tailored for the academic environment.

Keynote Speaker

Sunny Notani
Special Agent,
United States Secret Service
Presenters

Joe Torrieri
Director of Information Technology
Franklin Institute

Leonard Nelson, CCSP, CISA
Chief Information Security Officer Villanova University

Rob Rudloff, CISSP, CCSP, PCIP, CMMC RPA
Cybersecurity Services Rubin Brown, LLC Former CISO University of Denver

Isaac Abbs
Assistant Vice Chancellor for IT
CIO
Pima Community College

Javier Gonzalez, CISSP, CISA
Chief Information Security Officer
SecureX Higher Education

Rochelle Newton, EdD,EMPA,PMP
Former IT Leader Duke University

Paul M. Smith, MBA, CRISC, CCSP, CISM, CISSP
Director Network Connectivity and Monitoring CSL Former Assistant Director Network Security – Temple University

Suzanne Elhorr, CIAM
Risk Manager
American University of Beirut

Dieter Schuller
Entrepreneur and Technology Business Leader Identity and Access Management

Brian Cornell, SSGB, ITIL, CIPP
Chief Information Officer OculusIT – Higher Education Former CIO/CISO Elmira College
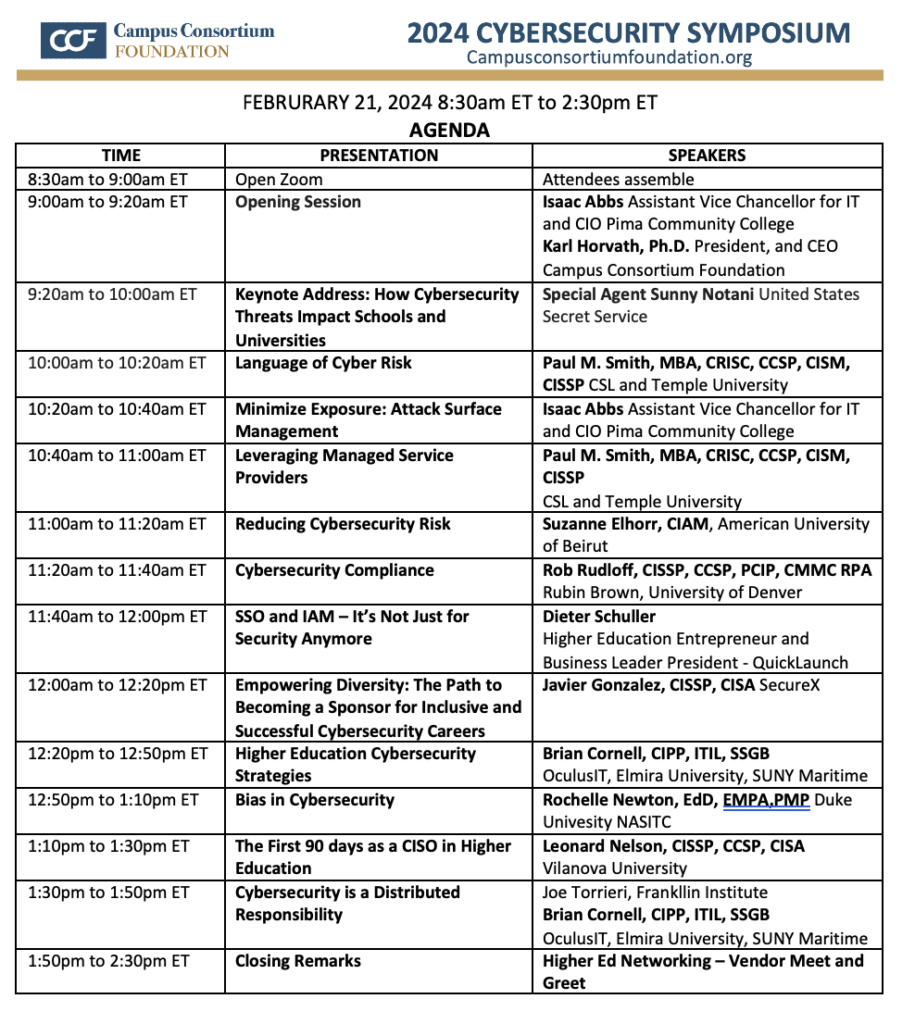
09:00 am to 9:20 am
Opening Session
• Welcome and Introduction
9:20 am to 10:00 am
Keynote Address
• How global cybersecurity threats impact education.
10:00 am to 12:00 pm
Presentations
• Higher Education Risk and Information Systems Control
• Managed Services and Cybersecurity
• Reducing Cybersecurity Risk
• Higher Education Cybersecurity Controls and Policies
• Identity, Access and Cybersecurity
12:00 pm to 1:30 pm
Presentations
• Empowering Diversity: The Path to Becoming a Sponsor for Inclusive and Successful Cybersecurity Careers
• Higher Ed Cybersecurity Strategies
• Cybersecurity and Diversity
• The First 90 days as a CISO in Higher Education
1:30 pm to 2:10 pm
Panel Discussion
• Higher Education Cybersecurity Exchange
• Closing Remarks and resources
2:10 pm to 2:30 pm
Interactive Session
• Vendor Meet and Greet
• Higher Education Cybersecurity Practices
Why Attend

Stay Ahead of Emerging Threats:
Proactively strengthen defenses against evolving risks.

Enhance Security Awareness and Education:
Foster a culture of security and informed decision-making.

Network with Peers and Experts:
Cutting-Edge Technologies and Solutions:
Interact with vendors and evaluate potential security products.
Request For Conference Full Access Video
Vendors